在 Ubuntu 18.04 里安装 Magento 2.2.6
当前最新 Magento 2.2 版本,不支持Ubuntu 18里默认的php7.2版本,可以考虑安装php7.1。
过程:
1.apt install oftware-properties-common # 准备安装第三方软件源
2.add-apt-repository ppa:ondrej/php # 选择这作为php7.1安装源
3.apt update # 更新软件源
4.apt install apache2 # 安装apache
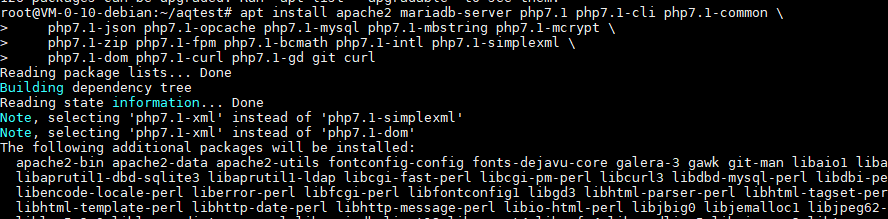
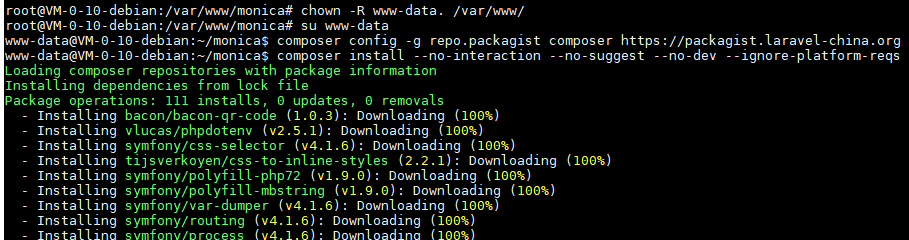
5.apt install mariadb-server php7.1 php7.1-fpm php7.1-common php-pear php7.1-curl php7.1-gd php7.1-mbstring php7.1-zip php7.1-mysql php7.1-xml php7.1-bcmath php7.1-soap php7.1-intl php7.1-mcrypt # 安装 php-fpm 和 mariadb 数据库
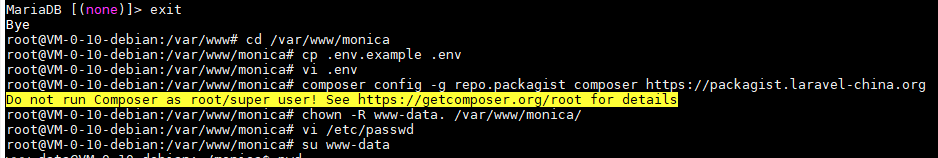
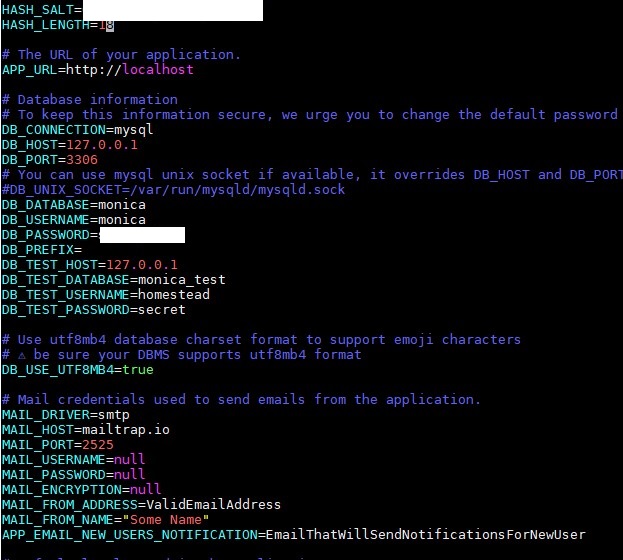
6.创建数据库,数据库用户,给magento2使用
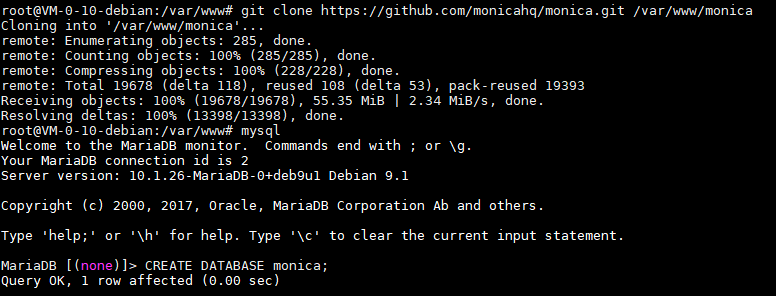
mysql
CREATE DATABASE monica;
CREATE USER 'magento2'@'localhost' IDENTIFIED BY 'mimamima';
GRANT ALL ON magento2.* TO 'magento2'@'localhost';
exit7.上传Magento文件,解压到 /var/www/html/magento2 目录
8.chown -R www-data. /var/www/html/magento2 # 设置文件权限
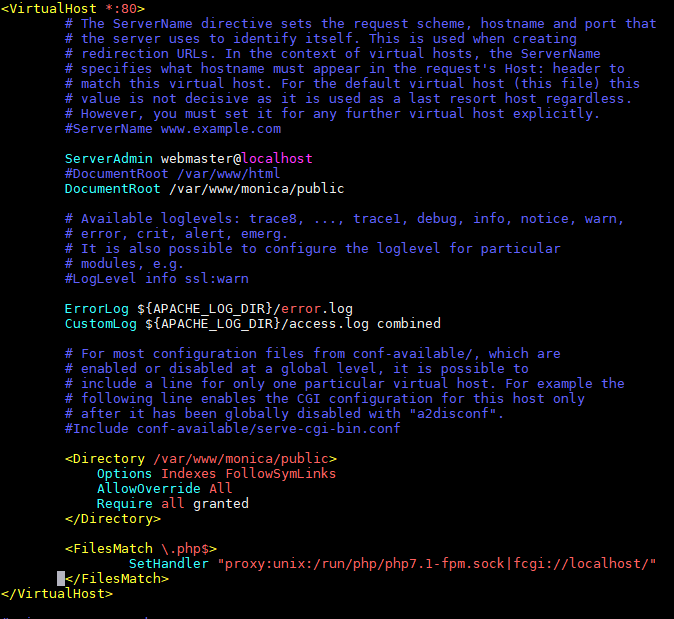
9./etc/apache2/sites-enabled/000-default.conf # 配置站点
# 更改默认站点的配置文件,文件路径设置为
DocumentRoot /var/www/html/magento2
# 添加目录配置内容
<Directory /var/www/html/magento2>
Options Indexes FollowSymLinks
AllowOverride All
Require all granted
</Directory>
# 添加php文件处理
<FilesMatch \.php$>
SetHandler "proxy:unix:/run/php/php7.1-fpm.sock|fcgi://localhost/"
</FilesMatch>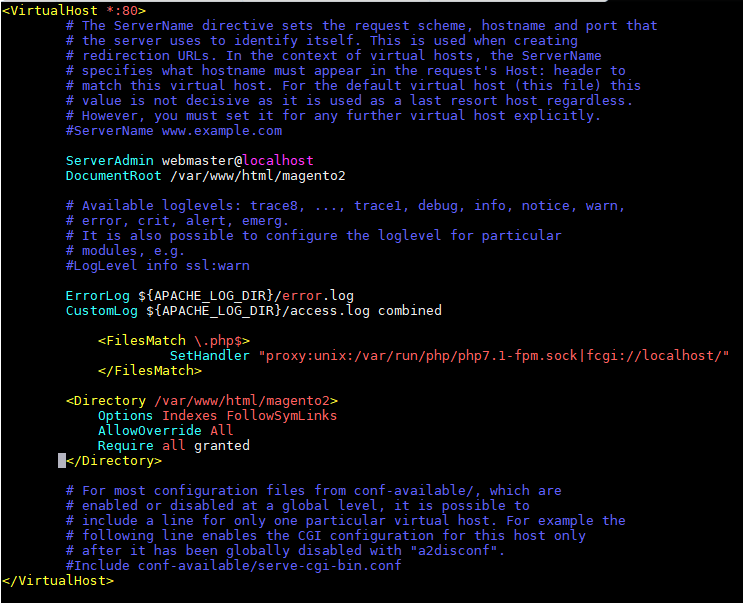
10.a2enmod rewrite proxy_fcgi # 启用 apache 的 rewrite 和 fcgi 模块
11.systemctl restart apache2 # 重启 apache
12.在浏览器里开始magento安装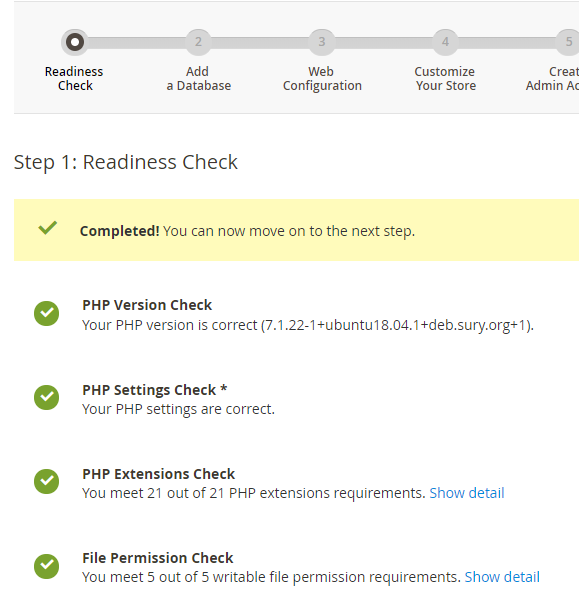
13.顺利安装,首页和后台测试正常
参考: